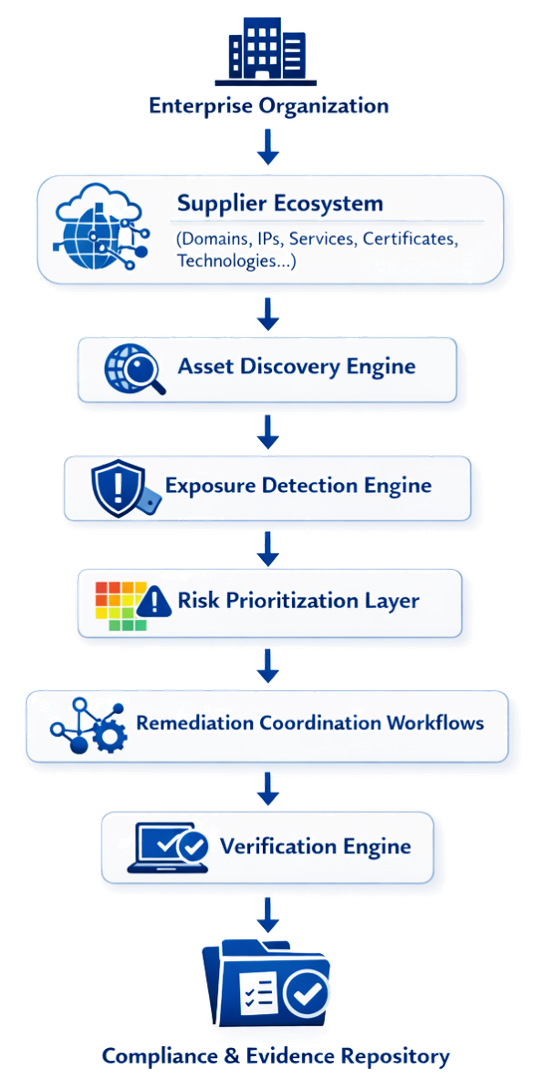
The CyTrusted platform is a fully SaaS, AI-native architecture designed to continuously manage supplier cyber risk at scale.
It ingests supplier ecosystem data (domains, IPs, services, certificates, technologies) and processes it through distributed asset discovery and exposure detection engines, ensuring broad and scalable coverage.
An intelligent risk prioritization layer focuses efforts on the most critical exposures, while AI-driven remediation workflows coordinate actions with suppliers.
A verification engine re-tests fixes to confirm resolution, and all results are consolidated into a secure compliance and evidence repository.
The platform is built for high security, scalability, and continuous operation, delivering automated risk assessments, remediation tracking, and audit-ready reporting.